What is CESR?
The Carolina Enclave for Secure Research (CESR) is a secure, centralized service for faculty and researchers that work with regulated research data. CESR meets the high-water mark of security standards to ensure that restricted information is protected per local, federal, and international laws while ensuring data confidentiality, integrity, and availability.
Benefits
Provides Security and Privacy Protection: The environment protects the integrity of sensitive data by complying with the most up-to-date requirements and standards.
Allows for Custom Analytical Software: The service allows for complete flexibility of the environments allowing for the tools researchers need.
Reduces Cost: A shared central enclave implementation reduces cost for individual researchers and departments.
Enables Secure Interdisciplinary Collaboration: Provides necessary secure workflow and dataflow for sharing protected information in large interdisciplinary projects.
Managed by University IT Professionals: CESR is professionally managed and operated. This allows researchers to focus on their research and analysis and avoid the expensive and time-consuming process of building and operating a secure environment themselves.
Optimizes Research Time: Having an existing secure research environment optimizes timelines. Prep time can be shifted to research.
Offers Collaboration with Research Computing: RC’s computational scientists are available to provide their expertise and help researchers
optimize workflows and unlock new ways to analyze the data.
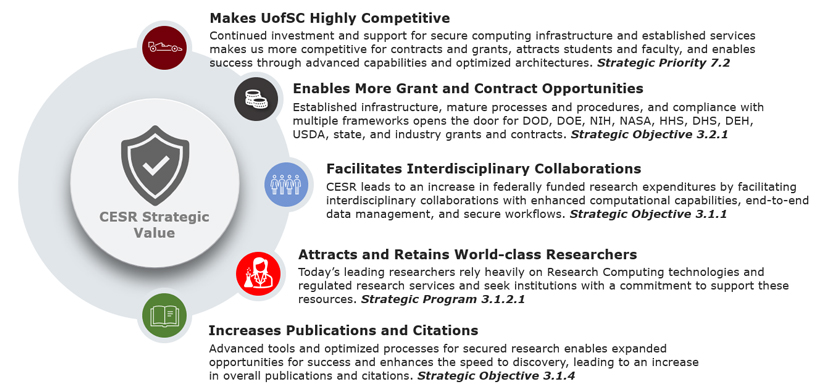
Strategic Value
Regulated Data Types
Researchers can securely store and work with:
- Electronic protected health information (ePHI) (HIPAA)
- Export-controlled data (ITAR/EAR)
- Controlled unclassified information (CUI)
- Intellectual property data (IP)
Core Technical Capabilities
Secure Data Storage
- Encrypted File Storage
- Secure File Sharing
- Enterprise class
- Backups
Computing Resources to Analyze Research Data
- Secure Virtual Machines
- Scalable infrastructure
- Enterprise class
- Future HPC
Flexible Secure Workflow
- Pre-validated environment
- Flexible implementations built on core offering
- Secure data workflow, end-to-end data management
- Custom consulting services
